Cdn Cgi/l/email Protection
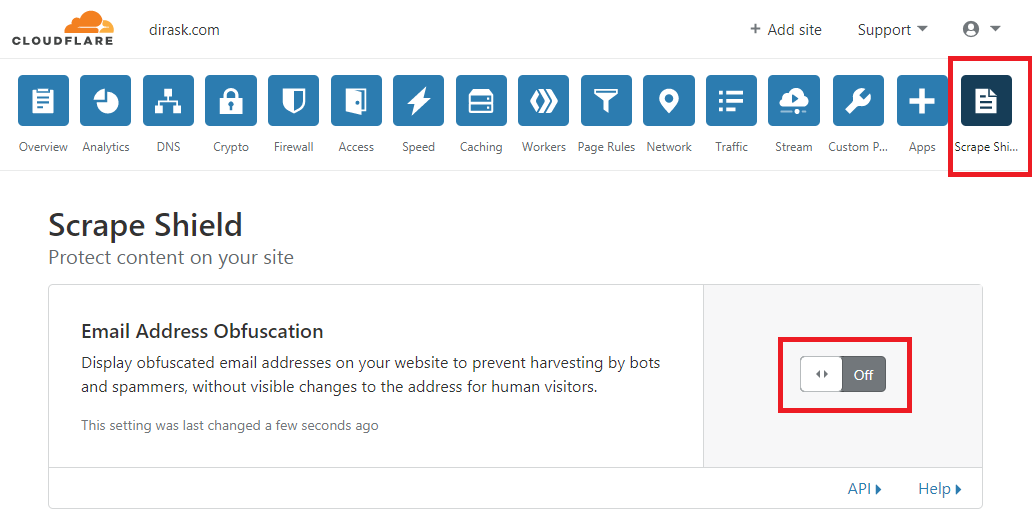
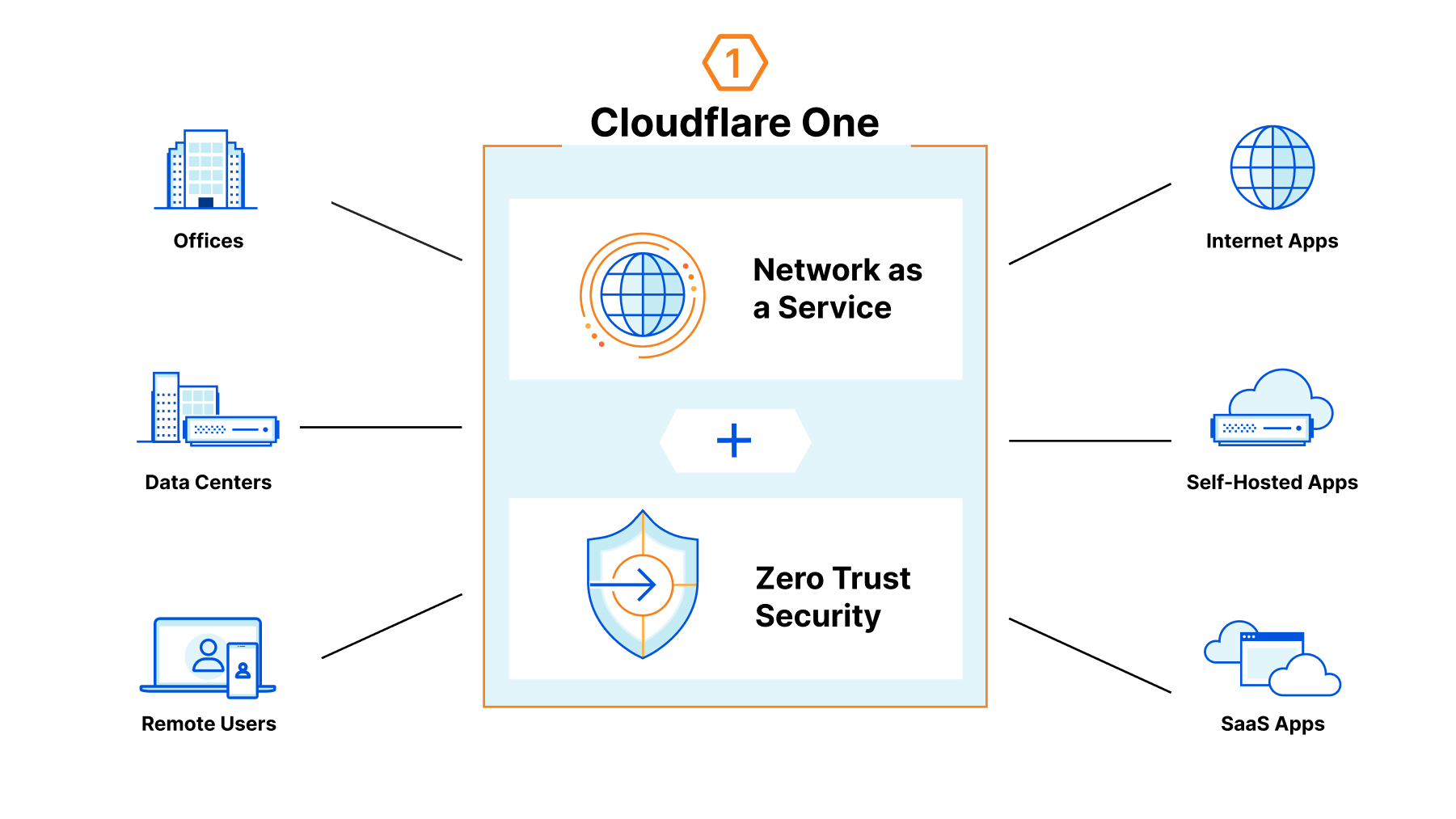
This is CloudFlare's dynamic email obfuscation. CloudFlare automatically apply the obfuscation to websites that they protect. If your website is protected by CloudFlare, you can turn the feature on by signing in to the dashboard then Cloudflare.com > ScrapeShield > Email Obfuscation. /cdn-cgi/ also can cause issues with various web crawlers. Search engine crawlers can encounter errors when crawling these endpoints and — though these errors do not impact site rankings — they may surface in your webmaster dashboard.. SEO and other web crawlers may also mistakenly crawl these endpoints, thinking that they are part of your site's content.
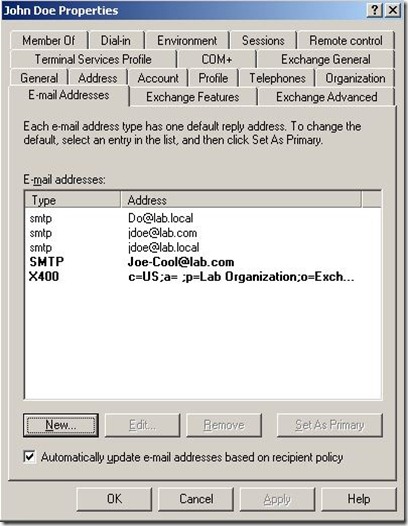
Stack Overflow for Teams Where developers & technologists share private knowledge with coworkers; Advertising & Talent Reach devs & technologists worldwide about your product, service or employer brand; OverflowAI GenAI features for Teams; OverflowAPI Train & fine-tune LLMs; Labs The future of collective knowledge sharing; About the company Visit the blog Then run the function using your email, picking a random number between 0-255: encodeEmail('example@example.org', 156); The hex encoded output is what we'll use in our website. The code to decode the email is is very similar. Decoding the email address.
Related Posts of Cdn Cgi/l/email Protection :
18+ Images of Cdn Cgi/l/email Protection

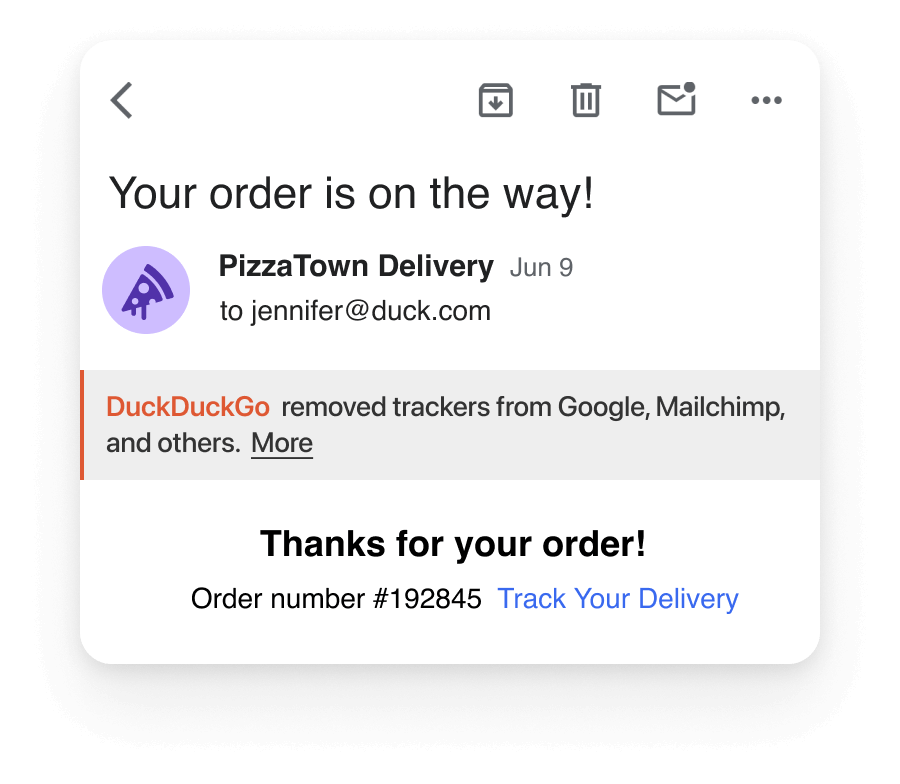
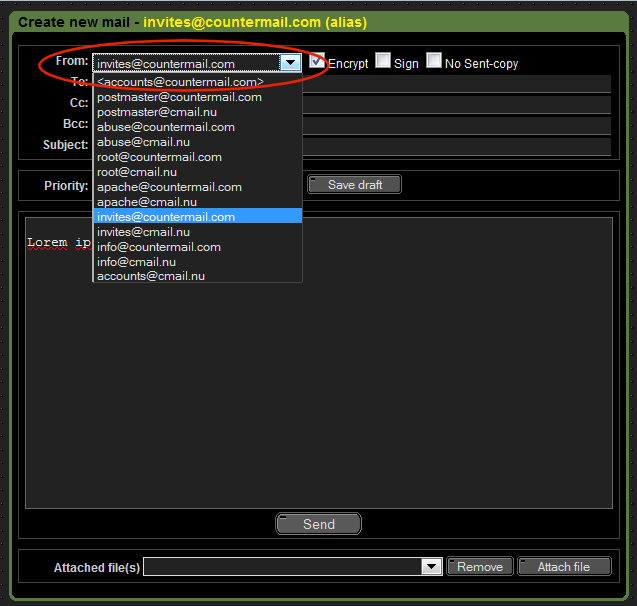
Email addresses on some websites are obfuscated by Cloudflare's Email Address Obfuscation Technique to prevent bots from scraping them while keeping them visible to humans. Any text that has been obfuscated using this method may be deobfuscated and returned to a human-readable format with the use of the cf-email-decode module.
It protects you from Email spam by hiding on-page emails and then using Javascript to decode them on page load. This technique protects emails from bots which cannot execute Javascript (but not from real browsers). In case you want your code to look beyond Cloudflare's email protection, you will have to decode the emails yourself.
As far as the changed email links, that is done by Cloudflare. If I visit that /cdn-cgi/l/email-protection URL on one of the other domain names, I see a message from Cloudflare explaining that they are trying to obfuscate email addresses. Cloudflare is a content delivery network (CDN) that uses servers all over the globe to proxy and cache.
Loading. It's quite likely that this protection was enabled at some point in the past as part of a bulk preset in the Cloudflare configuration. I've removed various such filters over the past months, putting things directly into our open content or public server configuration where possible to reduce vendor lock-in, or to remove them entirely.
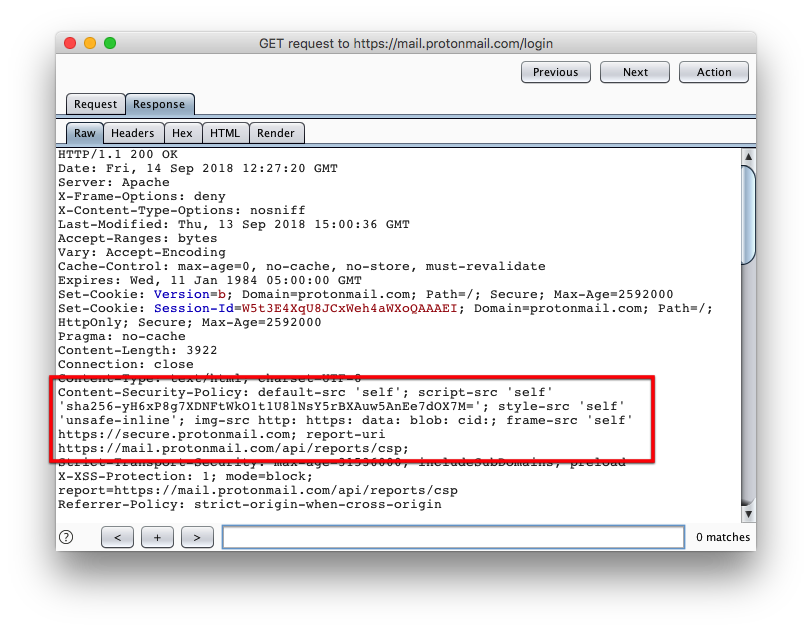
Ensure that anything under /cdn-cgi/challenge-platform/ is allowed. Your CSP should allow scripts served from your origin domain ( script-src self ). If your CSP uses a nonce for script tags, Cloudflare will add these nonces to the scripts it injects by parsing your CSP response header.
You are unable to access this email address allahleaks.com The website from which you got to this page is protected by Cloudflare. Email addresses on that page have been hidden in order to keep them from being accessed by malicious bots.
Modify CSP headers from the origin web server (except when using Zaraz, to ensure the Zaraz script is always running ↗). Require changes to acceptable sources for first or third-party content. Modify URLs (besides adding the /cdn-cgi/ endpoint and Cloudflare Fonts that rewrites Google Fonts urls). Interfere with locations specified in your CSP.
The other URL that started /cdn-cgi/l/email-protection was more of a mystery. I hadn't added anything in a /cdn-cgi/ folder! The fact that it contained a reference to a CDN was a clue, so I wondered if it was related to Netlify, but I couldn't think of an obvious reason why it would have any reference to emails. After a bit of quick.
Scroll to the very bottom of this article, and you'll see this:. For more information and ways to help fund the WWP delegation, contact [email protected]. If you click on "[email protected]", you'll be taken to a page that says:The website from which you got to this page is protected by Cloudflare.
Cloudflare Community
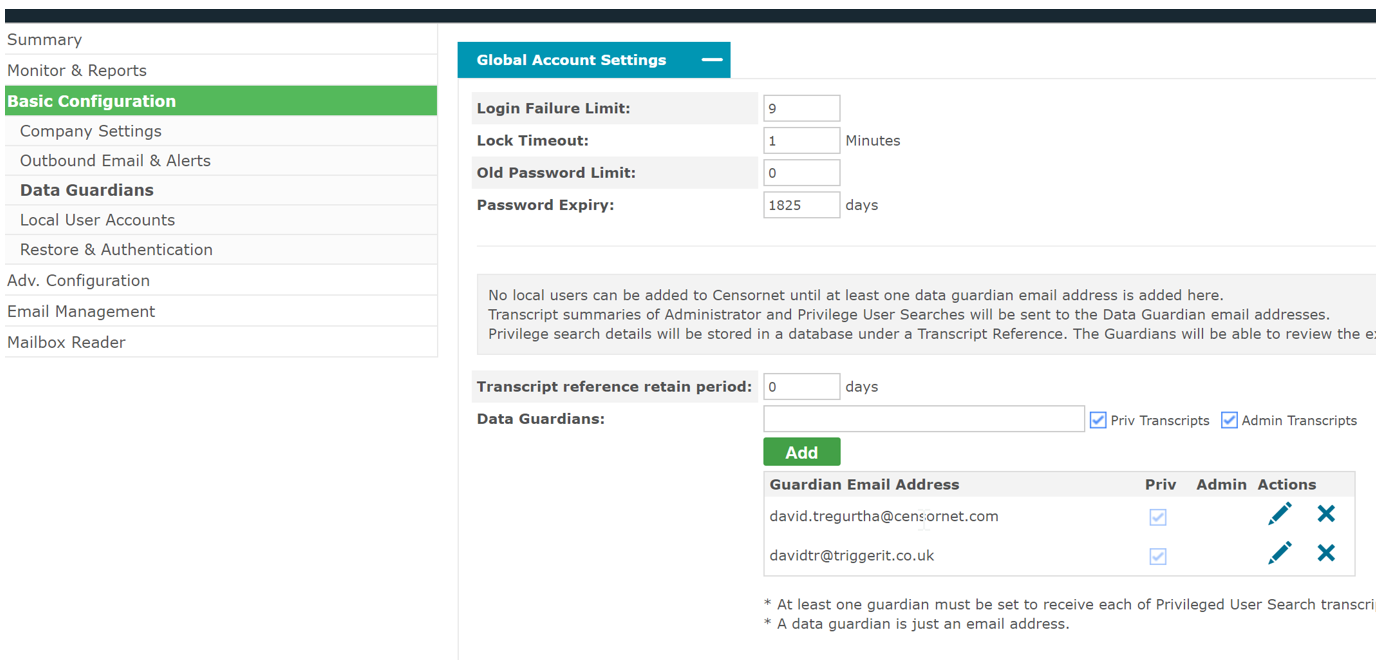
If, due to pressure from PCI, the website owner decides to start using Cloudflare, they gain a broad range of security features including DDOS protection, a Web Application Firewall (WAF), and email address obfuscation. These features are all enabled by default. Cloudflare's email address obfuscation works by scanning responses for email.
I've tried changing the link type to email and once saved it changes to [email protected]. When I click on this it shows that it is: Link Type: URL. Protocol: Other. URL: /cdn-cgi/l/email-protection. I'm getting some what annoyed with this as I wish to provide a support email address at the end of my messages.
This help content & information General Help Center experience. Search. Clear search
I noticed that GitHub appends a js that seems to remove links to email addresses when they have the string /cdn-cgi/l/email-protection with them. Any one else having this strange issue or is this even really from GitHub? Here is the prettified version of this script:
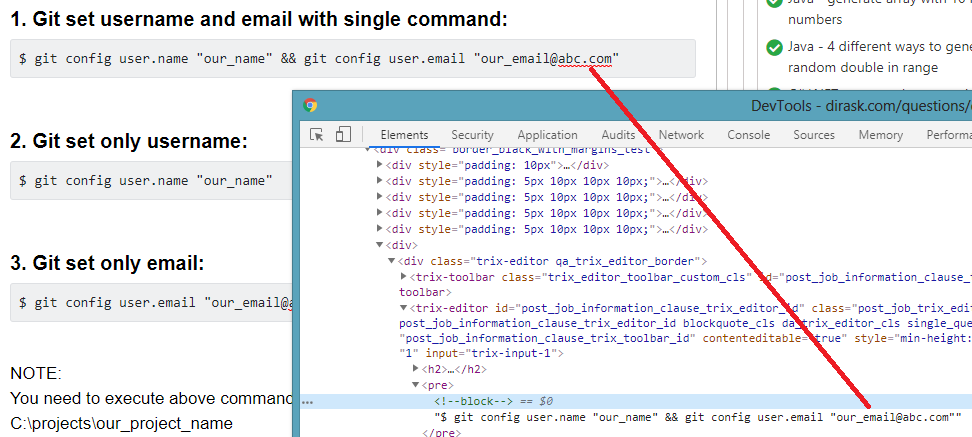
2、在Firefox浏览器中Email 右键->查看元素,很容易找到Email地址,如下图: 但是在网页源码中没有找到对应的Email地址,查看源代码如下: < html > < head ></ head > < body >
These are a part of CloudFlare's "Rocket Loader" feature. If you disable that feature, it should disable serving the bag files from cdn-cgi. edited Apr 17, 2017 at 18:55. answered Apr 17, 2017 at 18:46. Collin Barrett.
Gallery of Cdn Cgi/l/email Protection :
Cdn Cgi/l/email Protection - The pictures related to be able to Cdn Cgi/l/email Protection in the following paragraphs, hopefully they will can be useful and will increase your knowledge. Appreciate you for making the effort to be able to visit our website and even read our articles. Cya ~.




:format(webp)/cdn.vox-cdn.com/uploads/chorus_asset/file/23052942/VRG_Illo_4902_Security_hide.jpg)














:format(webp)/cdn.vox-cdn.com/uploads/chorus_asset/file/23052942/VRG_Illo_4902_Security_hide.jpg)